The global shift toward connected ecosystems is redefining how businesses operate, compete, and scale in a data-driven economy. From manufacturing floors to smart supply chains, organizations are rapidly adopting IoT solutions to unlock real-time visibility, automation, and predictive decision-making. This surge is driven by the growing need for operational efficiency, personalized customer experiences, and intelligent data utilization across industries.
However, while the benefits are compelling, the reality of adoption is far more complex. Businesses often face significant challenges in implementing IoT, including device integration, data fragmentation, security vulnerabilities, and infrastructure limitations.
The core challenge lies not in deploying IoT devices, but in effectively managing and integrating the massive volumes of data they generate. Without a scalable and well-structured integration framework, organizations face issues such as data silos, inconsistent analytics, and reduced operational efficiency, ultimately limiting the true potential of IoT technology.
This blog explores the key challenges in implementing IoT, including technical, operational, and security-related barriers. It also highlights practical solutions, integration strategies, and best practices that businesses can adopt to successfully overcome IoT implementation issues and build scalable, future-ready connected systems.
Key Takeaways
- IoT adoption is accelerating, driven by enterprise demand for automation, real-time insights, and data-driven decision-making.
- The biggest challenge lies in data integration, not device deployment, as managing large-scale IoT data is complex.
- Reliable connectivity is essential, since poor network coverage can disrupt device performance and operations.
- Scalability is a major concern due to fragmented platforms, diverse protocols, and evolving connectivity requirements.
- Security risks remain high, making encryption, authentication, and regular updates critical for protecting IoT ecosystems.
- Bandwidth and data overload issues can lead to latency, congestion, and reduced system efficiency.
- Interoperability challenges slow down implementation, as IoT systems often lack standardization across devices and platforms.
- Long-term success depends on strategy, including proper planning, scalable architecture, and ongoing maintenance.
Market & Statistics of IoT Implementation
- The global IoT market is expected to reach approximately $1.6 trillion by 2026, driven by enterprise adoption across industries such as manufacturing, healthcare, logistics, and smart infrastructure.
- The market continues to expand rapidly beyond this milestone, with projections indicating that the IoT industry could surpass $5.5 trillion to $12.6 trillion by 2030, reflecting strong long-term growth in connected ecosystems and digital transformation initiatives.
- The global IoT spending market is expected to exceed $1 trillion annually by 2026, underscoring enterprises’ heavy investment in IoT infrastructure, connectivity, and analytics to drive operational efficiency and innovation.
What is IoT?
The Internet of Things is a network of devices that collect data and transfer it to a network without human intervention. “Things” refers to the built-for-purpose nature of IoT devices. IoT data can originate from cameras or sensors connected to embedded systems, as well as from equipment such as gauges, scales, or other smart objects. Companies use IoT to gather more information about their operations. The data collected provides a better understanding of operations efficiency, customer behaviors and expectations, and decision-making processes. IoT technology is also employed to automate various business functions.
Key Challenge in Implementing IoT Systems 2026
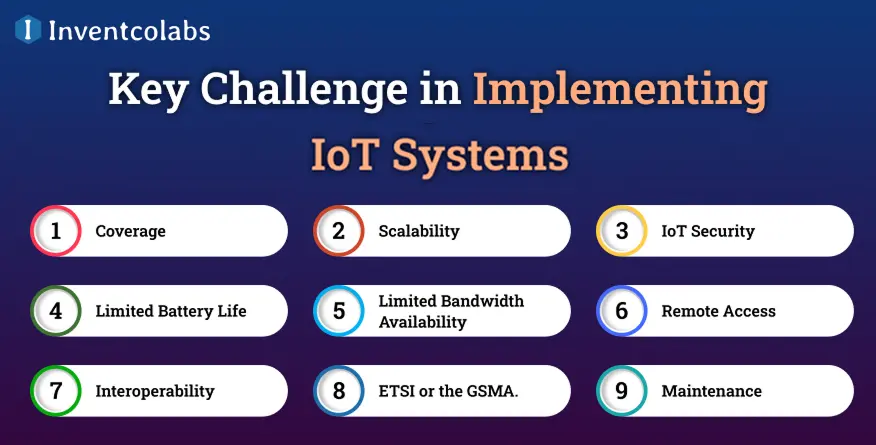
Developing IoT solutions poses many challenges. Solving these challenges is essential as the IoT market expands and more devices are installed, which could lead to security breaches.
1. Coverage
The network connection is crucial for an IoT operation. Without it, an IoT device will disappear from the market, significantly impacting your operations or essential services. Finding the ideal network for your business is a crucial component of due diligence, as some network choices severely restrict where IoT devices can be placed.
Some, for instance, may opt to utilize Wi-Fi for IoT connectivity; however, this could restrict the range of operation since devices will always have to be within a certain distance of the router hosting them. Locations that have a third site owner or pose problems due to security issues, or are complex and challenging for security to control credentials.
Wi-Fi is essential, but most Pure IoT or hybrid devices require Wi-Fi access due to manufacturing constraints or end-user requirements. For instance, remote-managed printers, local EV charge points, or payment systems usually require Wi-Fi as a primary or second connection.
This could cause problems due to geographical location, cost limitations, or required cases. For instance, the extra cost of a 5G or 4G modem is deemed prohibitive for the end-user. In the absence of the right infrastructure, no matter what connectivity mix is required, you’ll have to either equip all devices with a backup solution or invest in a reliable router and network security to ensure that dispersed devices remain connected.
2. Scalability
With more than 15 billion IoT devices worldwide, it’s not uncommon for an IoT Development Company to deploy thousands or hundreds of thousands of IoT devices worldwide. Every device will likely have its unique management platform that communicates with the firmware that it is running, connectivity technology and the global systems for support. These systems are private, making scaling mission-critical IoT operations challenging.
Scaling can be more challenging if your product must be fundamentally altered to accommodate the latest connectivity options. This decision requires consideration at the device or system design phase.
Scalability becomes even more complex when products need to be redesigned or updated to support evolving connectivity technologies such as 4G, 5G, LPWAN, or NB-IoT. These decisions must be addressed early at the device and system architecture stage to avoid costly rework.
Operators can have various contractual agreements that can result in significant differences in roaming costs and other oddities. A growing number of countries have banned permanent roaming, which means local profiles must be made available via in-the-air (OTA) for these restricted-access zones in the country (I.e., Turkey & Brazil).
Due to the roaming ban, problems can arise when you expand your business across different countries or within specific areas with permanent roaming restrictions. This concerns devices anticipated to travel internationally within such regions, i.e., logistics, transportation, and post-market Telematics.
3. IoT Security
IoT security issues are not new. Since the IoT was first made available, devices have been targeted by cyberattacks. Take, for instance, the famous Mirai Botnet case, which affected Linux devices, including routers and cameras. If a Custom IoT Development is compromised, the information it gathers could be obtained by a third party without the user’s consent. This could result in dire consequences, not just for businesses but also for consumers.
For instance, if a person or organization attempted to hack an IoT smart home/building/router system, they might gain access to private data. It could also include sensitive personal or commercial details, such as security credentials, bank account information, users’ email addresses, and home addresses. IoT devices and routers must be configured and connected for secure network access and managed only by systems with top-of-the-line security solutions, methodologies, and procedures.
Incorporating authentication, encryption, or tunneling security protocols into IoT devices will help protect them from cyberattacks. However, most IoT devices are limited in power supply, and implementing these mobile app security protocols could significantly increase the difficulty of deploying technological resources, the skills required to create and support these protocols, and the power requirements for simple transmissions.
As a result, many devices still need to integrate these features. Implementing at scale or providing complex connectivity solutions that involve multiple devices interconnected via local router infrastructure makes these aspects crucial. This is the most common situation when implementing branch or retail systems, and cameras are a must for security or privacy.
As technology and methods evolve, new IoT security threats are expected to be revealed. If you do not update your devices, you’ll find they become increasingly vulnerable to attack. This is why the law in England now requires connectivity for EV Charge Points, enabling crucial security and safety updates to be implemented quickly and safely.
4. Limited Battery Life
In the last IoT challenge, many IoT equipment had a short battery life. The batteries are usually tricky to recharge because they are placed on sites not owned by third parties or in remote areas. This makes it challenging to keep them running and functional.
This becomes a bigger problem when devices transfer large amounts of data through wireless connections or require regular software updates. However, larger batteries limit where devices can be placed or their reliability and usage, limiting their applications and diminishing their chances of effective scale.
If the battery were larger and utilized for predictive maintenance purposes in this scenario, it could make the device more challenging to implement in a plant or vehicle, making it more susceptible to the risk of hot temperatures or impact. Wearable devices for remote care or lone worker applications can become costly and unusable.
Another important aspect is that devices will spend most of their lives in remote locations with access to power. An incorrect network can lead to connectivity issues and shorten the device’s lifespan. Infrastructure is vital for every IoT operation. However, hosting multiple devices on the same network can cause delays, reduced performance, and higher latency.
This issue is compounded when dealing with critical applications like factory automation, sophisticated retail systems, and the medical Internet of Things (IoT). A network failure can have serious consequences, making it difficult for companies to ensure the provision of essential services.
5. Limited Bandwidth Availability
The volume of data generated by IoT devices is growing at an unprecedented scale and will continue to increase as device capabilities evolve. IoT devices are expected to generate nearly 80 zettabytes of data by 2026, accounting for a significant share of global data creation.
One of the most significant IoT-Wearable Connectivity Development issues they face is the limited bandwidth available due to their deployment in remote areas. This could make it difficult and costly to send all the data collected. As in any IoT operation, servers have to quickly sort and analyse the ever-growing volumes of data they’re confronted with.
However, if there are too many IoT devices and users within a given distance, it can cause network congestion, resulting in slower response times and lower performance.
6. Remote Access
There are a variety of IoT connectivity issues affecting devices deployed in remote areas. It could be due to limited access to sites and third-party ownership of devices, or to the inability to permit downtime during updates because of their security or critical nature. Many of these devices may not be able to access power or require specialised connectivity due to their distance or propagation requirements.
For a device to function in this kind of environment, many organizations rely on technical personnel who visit the location to help with the setup. This can be costly, time-consuming, and logistically challenging, particularly if the facility is located in a difficult-to-access location or is located out of the country.
Remote access options significantly reduce maintenance and support costs. These capabilities increasingly include the option to install local routers that can manage important devices and services independently and remotely in these kinds of locations.
7. Interoperability
One of the most essential IoT business issues that many service providers, and even you, might face is ensuring that your IoT products are in sync with one another and with your business applications. To adapt new software or hardware, you may need to implement changes across the chain to ensure your IoT operation aligns with the rest of the chain.
Although this isn’t the case for all IoT operations, another issue to consider is whether the technology used to develop the IoT solution is open source, proprietary, or compliant with major standards such as ISO, ETSI, or the GSMA.
8. ETSI or the GSMA
Without a designated regulatory body, the quality of software could be different because there is no universal standard that has to be followed, or in fact, it could make it more difficult for developers to partner with others in integrating essential services. Integrating new technology or functionality from multiple vendors, or setting up your IoT operations in a different location, can be challenging.
9. Maintenance
The final IoT business challenge on our list is maintaining IoT devices. Since these devices must be connected to the Internet regularly, they require ongoing maintenance to ensure their security and performance. In the most extreme cases, this could require manually updating every device with the latest patches and software improvements.
It can be costly and time-consuming, especially when many devices are spread across multiple geographic locations. The device’s connectivity also requires monitoring. The protection of mobile networks is a crucial aspect of device function and requires tracking and adjusting device performance to ensure they don’t frequently send signals in a jumble.
This type of signalling storm could be caused by devices that cannot connect for a brief period or by devices that fail. This is a severe issue for mobile operators. Devices malfunctioning or failing to utilize algorithms to distribute traffic may shut off a network.
With the ever-growing use of IoT devices over the past few years, older devices have begun to look like junk and if left on, could cause constant headaches. Many mobile operators are issuing kill commands to eliminate problematic older, outdated, inactive, or obsolete devices that are deemed a nuisance or a threat to the network.
Exploring Major Vulnerabilities in IoT Devices
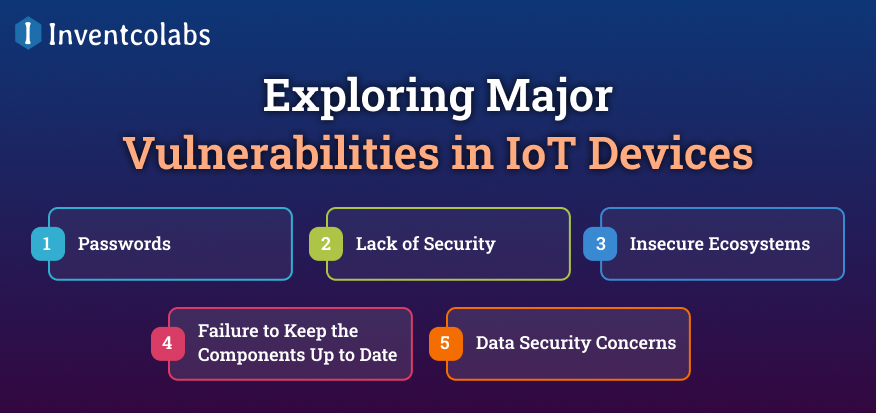
Understanding the vulnerabilities of IoT devices is increasingly vital as they continue to improve.
- Passwords: Simple ones can lead to unauthorized access to industrial equipment.
- Lack of Security: For networks, referred to as Man-in-the-Middle (MITM) attacks, exploits vulnerabilities in communication protocols and services running on IoT devices.
- Insecure Ecosystems: Components like the backend, web API cloud, and mobile interfaces should be protected by safe and reliable encryption methods.
- Failure to Keep the Components Up to Date: If components are not up to date with the latest software requirements or systems, the entire IoT ecosystem could be harmed.
- Data Security Concerns: The data stored must comply with privacy laws (GDPR or CCPA) to avoid legal penalties.
Importance of Encryption in Securing IoT Data
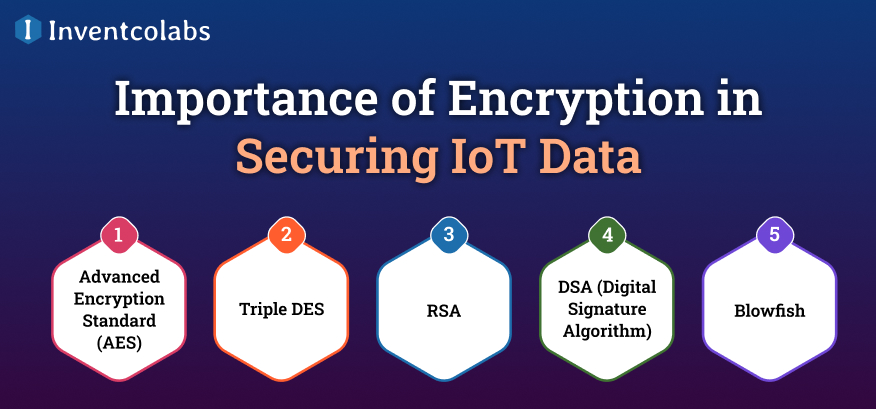
It is a key element in protecting IoT data due to the privacy issues inherent to IoT and the reality that IoT devices can be hacked without security and privacy protections in place.
IoT Development Company uses synchronous (single cryptographic key) and asynchronous (multiple cryptographic keys) methods to protect information. The most widely used techniques include:
- Advanced Encryption Standard (AES): An encryption algorithm used by security agencies and other organizations worldwide. It is easy to apply and implement across a variety of IoT security fields.
- Triple DES: DES is the successor to the DES algorithm (which is no longer in use). It is often used in payment systems and FinTech solutions.
- RSA: It is commonly used in SSL/TLS certifications, email encryption, and cryptocurrencies.
- DSA: It was developed in the late 1990s by the National Institute of Standards and Technology (NIST). It lets you create two digital signatures that enable the recipient to verify the sender’s authenticity.
- Blowfish: It is free and can be used to safeguard online transactions and user passwords.
How Inventco Helps You Overcome IoT Implementation Challenges?
Successfully implementing IoT requires more than just deploying connected devices—it demands a strategic, secure, and scalable approach. Inventco brings in-depth technical knowledge and industry experience to engage enterprises on the real-world challenges they face when implementing IoT across their value chains.
Even from the earliest planning stages, Inventco prioritizes laying a strong, robust foundation by implementing a scalable architecture and selecting appropriate connectivity services to ensure smooth integration with the system. This approach mitigates issues such as data silos, interoperability gaps, and infrastructure constraints.
Every solution we build is, by design, secure and reliable. To protect sensitive information and maintain network resilience against emerging cyber threats, Inventco deploys end-to-end encryption, secure device management procedures, and continuous monitoring frameworks.
Combining a successful method of delivery with post-production support, including rapid deployment, performance enhancement and long-term maintenance, Inventco gives businesses the capability to scale effectively while minimizing operational risk. With the power of innovation, Inventco enables organizations to achieve future-ready connected ecosystems by leveraging IoT and maximizing its full value through aligning technology with business.
Conclusion
The Internet of Things (IoT) is a rapidly evolving space, and billions of connected devices are revolutionizing sectors such as healthcare, logistics, and manufacturing. Though the advantages are high, businesses need to focus on important IoT implementation challenges especially in terms of security, interoperability and data integration. As adoption increases, robust security controls and active system monitoring are critical to protecting sensitive data and ensuring operational reliability.
And finally, a proper IoT implementation requires strategic planning, selecting the right technology stack, and working with expert development partners. These aspects allow for quicker mobilization, exposure to specialized knowledge, and lower operational risks. Organizations must also take a long-term view of IoT by understanding the complete IoT ecosystem, along with risks and infrastructure that it entails. By following a specific strategy, they can overcome implementation roadblocks and unleash the full potential of IoT-empowered innovation.
FAQ’s
Q1. What are the biggest challenges in IoT implementation?
Ans. The biggest challenges in IoT implementation include device integration, data management, security vulnerabilities, scalability issues, and connectivity limitations. Managing large-scale data and ensuring seamless communication between devices remain major obstacles for businesses.
Q2. Why is data integration important in IoT systems?
Ans. Data integration is crucial in IoT systems because devices generate massive volumes of data. Without proper integration, businesses face data silos, inconsistent analytics, and reduced efficiency, limiting the overall effectiveness of IoT solutions.
Q3. How can businesses overcome IoT security challenges?
Ans. Businesses can overcome IoT security challenges by implementing strong encryption protocols, multi-factor authentication, regular firmware updates, and continuous monitoring. These measures effectively help protect sensitive data and prevent cyberattacks across connected IoT ecosystems.
Q4. What role does scalability play in IoT implementation?
Ans. Scalability ensures that IoT systems can handle increasing numbers of devices and data without performance issues. A scalable architecture allows businesses to expand operations efficiently while maintaining system reliability and performance across connected environments.
Q5. How does connectivity impact IoT performance?
Ans. Connectivity is critical for IoT performance because devices rely on stable networks to transmit data. Poor connectivity can lead to data loss, delays, and system failures, significantly affecting real-time decision-making and overall operational efficiency.
Q6. How can businesses successfully implement IoT solutions?
Ans. Businesses can successfully implement IoT solutions by adopting a clear strategy, selecting scalable technologies, implementing robust security measures, and partnering with experienced development teams. Proper planning helps overcome challenges and maximize long-term business value.





