The healthcare industry is undergoing one of the most significant digital transformations in its history. From AI-powered diagnostics and remote patient monitoring to virtual care platforms and predictive health analytics, the demand for healthcare applications has never been more intense or more consequential. But with that opportunity comes a business reality that no founder, investor, or development team can afford to overlook: every application that touches patient data must navigate one of the most stringent regulatory frameworks in the world, the Health Insurance Portability and Accountability Act (HIPAA).
Consider the numbers. In 2025, the average cost of a healthcare data breach reached $7.42 million globally, the highest of any industry for 14 consecutive years. In the United States, that figure climbs to $10.22 million per incident. In 2024, over 275 million patient records were compromised across more than 700 large-scale breaches reported to the HHS Office for Civil Rights. For founders and investors backing healthcare technology, these are not abstract compliance statistics, they are existential business risks that have ended careers, shuttered companies, and destroyed patient trust.
At the same time, the global digital health market was valued at $288.55 billion in 2024 and is projected to reach $946 billion by 2030. The market rewards those who build correctly, and severely punishes those who don’t. HIPAA compliance is not a burden on development. It is the infrastructure that makes sustainable healthcare innovation possible, the prerequisite for enterprise healthcare sales, and increasingly a primary signal of product maturity in Series A due diligence.
Whether you are building a telemedicine platform, an EHR integration layer, a mental health application, or an AI-powered patient engagement tool, this guide covers everything you need to make the right decisions, from understanding what HIPAA actually requires of your technology, to the security safeguards and features your app must have, to the step-by-step build process, technology stack, AI integration challenges, cost structures, and how a purpose-built development partner accelerates your path to a compliant, market-ready product.
Development costs for HIPAA-compliant applications typically range from $10,000 to $100,000 or more, depending on complexity, integrations, and the depth of compliance. This guide will help you understand where every dollar goes, and why the investment is always smaller than the alternative.
Key Takeaways
- Healthcare data breaches average $7.42M globally in 2025, compliance is a core business investment.
- HIPAA penalties now range from $145 to $2.19M per violation under updated 2026 OCR enforcement guidelines.
- Building a HIPAA-compliant app MVP costs $30,000–$100,000+, scaling with complexity and integrations.
- Three HIPAA rules, Privacy, Security, and Breach Notification, directly govern every healthcare app.
- Encryption, audit trails, and role-based access control are the non-negotiable technical compliance foundations.
- Every third-party vendor handling PHI must have a signed Business Associate Agreement before integration.
- AI features in healthcare apps require additional de-identification protocols and BAA-covered compute infrastructure.
What Is HIPAA Compliance in App Development?
The Health Insurance Portability and Accountability Act (HIPAA) was enacted to protect the privacy of the American people and the management and exchange of health records. For application developers and startup medical professionals, HIPAA compliance means creating systems that provide the legal protections for the management of the most sensitive and private health information.
In the mobile app development process, HIPAA compliance is more than an option to check once build iterations are completed. It encompasses an architectural perspective that will determine the deployment of database systems, the implementation of API security protocols, and the selection of cloud infrastructure and third-party integrations. HIPAA should be treated as a design philosophy. Development teams regard compliance as a feature that needs to be addressed later in the development process and end up implementing costly rework two to three times more often.
Market Statistics Every Healthcare Founder Needs in 2026
- The average cost of a healthcare data breach reached $7.42 million globally in 2025, the highest of any industry for 14 consecutive years. U.S. specific breaches averaged $10.22 million, a 9.2% increase year-over-year.
- Over 275 million patient records were compromised in 2024 alone, across more than 700 large-scale breaches reported to the HHS Office for Civil Rights, including the Change Healthcare ransomware attack, which affected approximately 192.7 million individuals.
- The global digital health market was valued at $288.55 billion in 2024 and is projected to surge to $946 billion by 2030 (Grand View Research), creating the largest compliance-gated revenue opportunity in software development history.
The Three HIPAA Rules That Directly Govern App Development
Understanding HIPAA compliance begins with the three foundational rules that govern how patient data is handled in digital systems:
Privacy Rule: Defines what constitutes Protected Health Information (PHI), who is permitted to access it, and under what circumstances it may be used or disclosed. For developers, this translates into explicit consent workflows, minimum-necessary data access principles, and strict controls on how patient data is shared across the platform.
Security Rule: Mandates administrative, physical, and technical safeguards for electronic PHI (ePHI). It is the most technically demanding aspect of HIPAA for development teams, your encryption standards, access control architecture, audit logging infrastructure, and incident response procedures all originate here.
Breach Notification Rule: Requires covered entities to notify affected individuals within 60 days of discovering a breach of unsecured PHI. For developers, this means building breach detection systems and automated notification workflows into your application architecture, not as an afterthought, but as a core system capability.
Does Your App Need to Be HIPAA Compliant?
Founders often ask whether an app should be HIPAA-compliant. It varies by app, and getting this answer wrong can be costly. If you exceed compliance for apps that don’t handle PHI, that money could go to better uses. If you offer compliance for an app that handles PHI, the business is exposed to HIPAA fines that can reach $2.19 million per violation category under the OCR 2026 enforcement guidelines. It will also expose the organization to liability for the intentional misuse of PHI.
You should first consider if your app creates, receives, maintains, or transmits PHI. Ultimately, if your app does work for a covered entity, it must remain HIPAA-compliant.
Apps That Always Require HIPAA Compliance
- Telemedicine and virtual care platforms
- Electronic Health Record (EHR) and Electronic Medical Record (EMR) systems
- Remote patient monitoring and connected medical device applications
- Patient portals that display or accept clinical data
- Mental health platforms that collect treatment-related information
- Lab result delivery and diagnostic tools
- Prescription management and pharmacy applications
- Medical billing, claims processing, and healthcare payment software
- AI-powered diagnostic tools and clinical decision support systems
Apps That May Require Compliance Depending on Use
- Fitness trackers that connect to clinical systems or transmit data to providers
- Wearable device apps that send physiological data to healthcare organizations
- Appointment scheduling tools integrated with medical record systems
- Population health management and care gap identification platforms
- Insurance comparison tools that process health-related personal data
Apps That Are Generally Exempt
- General wellness and fitness apps that do not interact with clinical data or covered entities
- Nutrition and diet tracking apps are not connected to any healthcare provider system.
- Meditation and general mental wellness apps with no clinical integration or PHI
- Employee wellness programs that collect only anonymized aggregate health data
Why This Decision Matters More Than Ever in 2026?
In 2026, the Office of Civil Rights integrated risk management into its enforcement. This now means that organizations, in addition to documenting risks, must demonstrate they have a plan to address them.
There has been a 40% increase in enforcement actions of HIPAA violations by state attorneys general since 2023. By January of 2026, OCR closed 11 investigations related to hacks, each of which will have financial penalties. In 2025, the average settlement for HIPAA violations was $1.2 million.
For founders, this means the cost of compliance is becoming more favorable than the cost of noncompliance. It is always more cost-effective to integrate compliance from the beginning of product development than to add it later, both in terms of development costs and regulatory risks.
Key HIPAA Technical & Security Safeguards Your App Must Meet
HIPAA’s Security Rule organizes its requirements into three categories of safeguards. Each category contains specific standards and implementation specifications, some required, others addressable (meaning you may implement alternatives that accomplish the same security objective, provided you document your reasoning). For development teams, the Technical Safeguards represent the highest concentration of specific engineering requirements.
1. Administrative Safeguards
Administrative safeguards are the policies, procedures, and workforce management practices that govern how PHI is protected within your organization:
- Conducting and documenting a thorough security risk analysis and maintaining an active risk management program.
- Designating a HIPAA Security Officer responsible for security policy development and compliance oversight.
- Implementing workforce training on security procedures, acceptable use, and PHI handling requirements.
- Establishing access management protocols for personnel onboarding, role changes, and offboarding.
- Creating and maintaining a contingency plan covering data backup, disaster recovery, and emergency access procedures.
- Evaluating and documenting Business Associate relationships for every third-party vendor handling PHI.
2. Physical Safeguards
Physical safeguards govern access to the systems and devices that store and process ePHI:
- Facility access controls limiting unauthorized physical entry to server rooms or data storage environments.
- Workstation uses policies defining appropriate physical settings and practices for accessing ePHI.
- Device and media controls covering handling, transfer, disposal, and reuse of any media containing PHI.
- Mobile device management (MDM) protocols for applications deployed on smartphones or shared clinical devices.
3. Technical Safeguards
Technical safeguards place the heaviest requirements on the development team:
- Access Controls: Unique user identification for every system user, emergency access procedures, automatic session logoff, and encryption and decryption capabilities for ePHI.
- Audit Controls: Hardware, software, and procedural mechanisms to record and examine all activity in systems that contain or use ePHI. Logs must be tamper-evident, attributable to individual users, and retained for at least 6 years.
- Integrity Controls: Mechanisms to protect ePHI from improper alteration or destruction, including error-correcting memory, hash verification, and data validation on all PHI write operations.
- Transmission Security: Technical measures that protect ePHI during electronic transmission across networks, including encryption and network monitoring.
4. Transmission Security Standards
Any ePHI transmitted over a network must be protected against unauthorized interception. In practice, this means:
- TLS 1.3 for all API communications (TLS 1.2 as minimum floor; 1.0 and 1.1 are no longer acceptable).
- AES-256 encryption for all data at rest across databases, backups, and cached storage.
- End-to-end encryption for any messaging, file transfer, or data sharing features.
- No transmission of PHI through standard email or SMS channels without additional encryption layers.
- Certificate pinning for mobile applications to prevent man-in-the-middle attacks.
Must-Have Features of a HIPAA-Compliant App

Building a HIPAA-compliant application requires foundational capabilities to meet the basic requirements and the advanced security capabilities to protect your application against 2026’s advanced cyber threats. Below are the key features of a HIPAA-Compliant healthcare app:
1. Encrypted Data Storage
Healthcare applications must use advanced encryption standards, such as AES-256, to encrypt all stored PHI. Secure key management, decryption access, and controlled encrypted backup storage minimize the risk of exposure to breaches and the compliance risks associated with them.
2. Secure User Authentication
An application that adheres to HIPAA requirements should employ strong authentication systems, including MFA, biometric login, password policies, and account lockout protections, and these systems should all work to ensure the user is authenticated before any sensitive PHI is disclosed.
3. Role-Based Access Control (RBAC)
RBAC provides a mechanism to limit access to healthcare data and to divide users into groups, including, but not limited to, doctors, nurses, and patients. This practice follows the minimum necessary access guidance and prevents unauthorized exposure of PHI.
4. Comprehensive Audit Trails and Activity Logs
It is a requirement for healthcare applications to log any access, alterations, and removals of PHI. Audit logs must be tamper-proof for compliance and for both security monitoring and HIPAA’s record retention requirements.
5. Automatic Session Timeout
Automatic session timeouts promote secure PHI access to unattended and shared clinical systems by requiring re-authentication and invalidating sessions. The risks associated with inactive and abandoned healthcare application sessions are minimized.
6. Breach Detection and Notification System
The HIPAA mandates that organizations identify and promptly respond to such occurrences. Key elements include breach investigations and notifications to regulatory authorities. Automated workflows support anomaly detection and breach response, meeting these requirements.
7. End-to-End Encrypted Messaging
Protection of PHI during communication is ensured by end-to-end encryption in healthcare messaging systems. The secure messaging infrastructure supports the provision of audit logs necessary for HIPAA compliance and transparent communication in the healthcare sector.
8. Business Associate Agreement (BAA) Management Module
Healthcare applications must track all vendors that handle PHI and maintain up-to-date BAAs. Centralized BAA management improves visibility into compliance, vendor accountability, renewal tracking, and enterprise healthcare audit preparedness across integrated systems.
9. Data Anonymization and De-identification Engine
De-identification tools remove patient identifiers, as defined by HIPAA, before analytics and AI systems are used. Reporting, machine learning, and healthcare research can be conducted without exposing personally identifiable patient information.
10. Zero-Trust Network Architecture
The zero-trust security model uses the principle of least privilege and grants access to those entities that require it. Healthcare cybersecurity is enhanced through segmentation and continuous monitoring because zero-trust networks do not automatically trust internal networks.
11. Emergency Access Protocols
Healthcare solutions must include systems for emergency or ‘break-glass’ access for time-sensitive clinical situations, allowing PHI to be accessed in emergencies while supporting audits, investigations, and compliance evaluations after access.
12. Automated Compliance Reporting Dashboard
Automated compliance dashboards improve healthcare reporting and simplify enterprise audits. They consolidate compliance metrics, audit trails, and provide instant access to security assessments and healthcare reporting to mitigate reliance on manual reporting.
How to Build a HIPAA-Compliant App: Step-by-Step Process
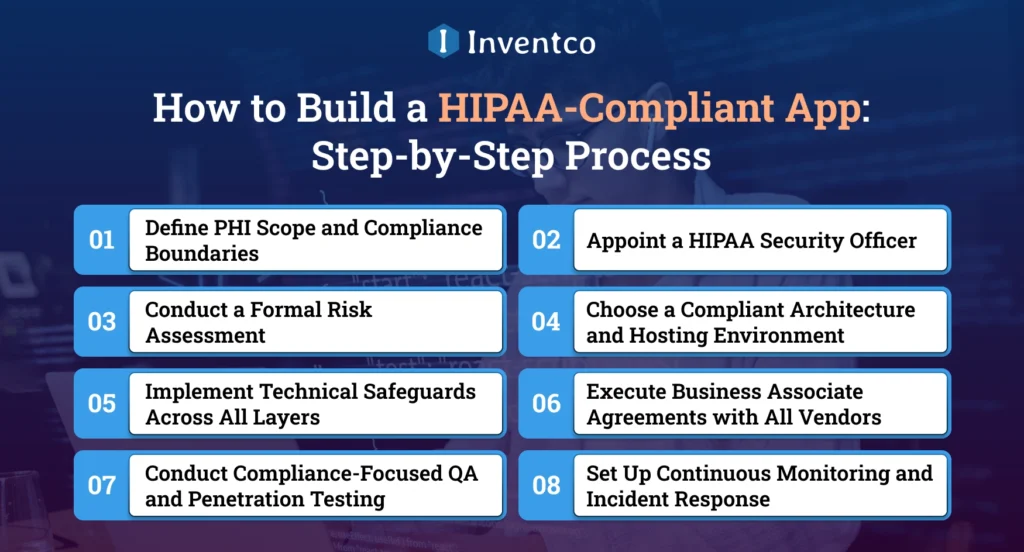
Building a mobile app for the healthcare industry, which is HIPAA-compliant, is a disciplined engineering process that requires compliance to be embedded at every stage of development, not appended at the end. Development teams that treat HIPAA as a final checklist consistently spend two to three times more on remediation, and often delay launch by months, compared to teams that establish compliance architecture before the first sprint. The eight-step process below reflects how Inventco approaches every healthcare application engagement.
Step 1: Define PHI Scope and Compliance Boundaries
Before development begins, healthcare teams must identify all PHI collected, processed, stored, or transmitted within the application. A complete PHI data map helps define compliance boundaries, security requirements, encryption needs, API access rules, and third-party vendor obligations across the entire healthcare ecosystem.
Step 2: Appoint a HIPAA Security Officer
Every HIPAA-compliant healthcare project requires a designated Security Officer responsible for compliance oversight, risk management, policy enforcement, staff training, and audit preparation. This role ensures accountability, maintains documentation, and manages communication during OCR investigations, security incidents, or ongoing regulatory compliance reviews.
Step 3: Conduct a Formal Risk Assessment
Healthcare organizations must identify vulnerabilities affecting the confidentiality, integrity, and availability of PHI. Risk assessments evaluate infrastructure, codebases, vendors, workforce risks, and cybersecurity threats, and create documented remediation plans that align with HIPAA’s active risk management and compliance requirements.
Step 4: Choose a Compliant Architecture and Hosting Environment
Selecting HIPAA-eligible cloud infrastructure, such as AWS, Azure, or GCP, strengthens healthcare application security and compliance. Teams must implement secure backups, disaster recovery systems, network segmentation, encryption, infrastructure-as-code practices, and scalable architectures supporting long-term healthcare data protection and operational reliability.
Step 5: Implement Technical Safeguards Across All Layers
Healthcare applications must deploy technical safeguards, including AES-256 encryption, TLS-secured communication, MFA, RBAC, audit logging, session timeouts, API security, and vulnerability protection. Every safeguard should be documented, tested, and mapped directly to HIPAA technical security requirements and implementation standards.
Step 6: Execute Business Associate Agreements with All Vendors
Every vendor handling PHI must provide a signed Business Associate Agreement before integration begins. This includes cloud providers, analytics platforms, monitoring tools, AI services, and communication systems. Proper BAA management reduces third-party compliance risks and improves audit readiness across healthcare ecosystems.
Step 7: Conduct Compliance-Focused QA and Penetration Testing
HIPAA compliance testing extends beyond functionality and includes penetration testing, vulnerability assessments, encryption validation, RBAC verification, session management testing, and audit log reviews. Continuous security testing identifies weaknesses early and supports ongoing healthcare cybersecurity compliance and enterprise procurement requirements.
Step 8: Set Up Continuous Monitoring and Incident Response
Healthcare applications require real-time monitoring systems to detect suspicious activities, unauthorized access attempts, and indicators of breaches. Organizations must maintain documented incident response plans covering escalation procedures, evidence preservation, breach notifications, forensic analysis, and post-incident remediation to ensure long-term HIPAA compliance readiness.
HIPAA-Compliant App Development Cost
Building a HIPAA-compliant healthcare app requires additional investment in security infrastructure, encryption, audit logging, compliance monitoring, and PHI protection. Depending on complexity, healthcare app development costs typically range from $10,000 to $100,000+, with HIPAA compliance increasing overall costs by 20–35%.
Basic Healthcare App: $10,000–$25,000
Includes simple healthcare applications with appointment booking, patient registration, secure login, notifications, and basic HIPAA-ready security features. Ideal for startups validating healthcare ideas with limited integrations, minimal workflows, and MVP-level functionality.
Telehealth Platform: $25,000–$60,000
Covers virtual consultation platforms with video calling, scheduling, secure messaging, e-prescriptions, and patient management features. Costs increase with HIPAA-compliant video infrastructure, payment gateways, multi-user dashboards, and third-party healthcare integrations.
Remote Patient Monitoring App: $40,000–$80,000
Designed for wearable device integration, real-time health tracking, alerts, and patient monitoring dashboards. Development costs rise with IoT connectivity, cloud infrastructure, analytics, continuous data streaming, and advanced security compliance requirements.
EHR/EMR or AI-Powered Healthcare App: $100,000+
Enterprise-grade platforms require complex workflows, clinical data management, AI-driven analytics, predictive healthcare insights, and interoperability standards like FHIR or HL7. Higher costs reflect advanced security, scalability, integrations, and regulatory compliance needs.
Tech Stack for HIPAA-Compliant Mobile App Development
For HIPAA-compliant mobile app development, various tech stacks are at your disposal. However, from a compliance standpoint, it is essential to use the right technologies from an architectural perspective, in line with the regulation’s requirements, so that each component has built-in protections for auditability and PHI protection. Also, you will need to examine the BAA offered by third-party-compliant services.
Cloud Platforms
- Amazon Web Services, Microsoft Azure, and Google Cloud Platform offer HIPAA-eligible services with signed BAAs.
- Secure healthcare infrastructure on these platforms enables analytics, FHIR integration, and deployment.
Databases & Storage
- PostgreSQL, Amazon RDS, Azure SQL, and MongoDB Atlas provide encrypted PHI storage with audit logging.
- Secure cloud storage solutions like Amazon S3 and Azure Blob Storage ensure tamper-resistant backup retention.
Frontend & Backend Frameworks
- React Native, Flutter, Swift, and Kotlin support the development of secure healthcare mobile applications.
- Backend frameworks, including Node.js, Django, FastAPI, and Spring Boot, enable scalable HIPAA-ready architectures.
Security & Compliance Tools
- AWS KMS, Okta, CloudTrail, and Snyk strengthen encryption, authentication, monitoring, and vulnerability management.
- Every third-party healthcare integration must provide a signed BAA before processing PHI.
HIPAA and AI: What Changes When You Add Machine Learning?
Artificial intelligence is reshaping healthcare applications through predictive analytics, virtual assistants, diagnostic support, and personalized patient engagement. However, integrating AI into healthcare systems introduces new HIPAA compliance challenges, especially when machine learning models process Protected Health Information (PHI).
AI and PHI Exposure
AI models often rely on clinical datasets containing sensitive patient data. Training datasets, inference requests, embedding vectors, and AI-generated outputs can all expose PHI if not properly secured.
De-Identification Requirements
HIPAA allows AI training through:
- Safe Harbor Method: Removes all 18 HIPAA identifiers.
- Expert Determination Method: Uses statistical validation to minimize re-identification risks.
Compliance for AI Features
- AI chatbots and LLMs must operate on HIPAA-eligible infrastructure with signed BAAs.
- Predictive analytics and clinical AI tools must follow minimum-necessary data access principles.
- AI-driven clinical decision tools may also require FDA SaMD compliance review.
Testing and Maintaining HIPAA Compliance Over Time
HIPAA compliance is not a milestone you achieve at launch, it is an operational discipline you maintain through every product sprint, infrastructure change, third-party integration, and regulatory update. The most common source of HIPAA violations in mature healthcare products is not the initial build, it is the accumulation of small compliance gaps introduced through product updates that were not reviewed against security requirements before release.
Continuous Compliance Monitoring
- HIPAA compliance requires ongoing security reviews, audits, and infrastructure monitoring beyond the initial product launch.
- Regular assessments help identify compliance gaps before they become security risks.
Compliance Audits
- Internal audits verify access controls, BAAs, risk assessments, and staff security training.
- Third-party healthcare security audits and HITRUST certifications strengthen enterprise trust and compliance validation.
Security Testing
- Monthly vulnerability scans and continuous dependency monitoring reduce cybersecurity risks.
- Annual penetration testing and red team exercises help identify critical security weaknesses.
Data Breach Response
- HIPAA requires breach notifications within 60 days of discovery.
- Organizations must isolate affected systems, assess PHI exposure, notify impacted users, and report incidents to HHS when required.
Maintaining Compliance During Product Updates
- Every PHI-related feature should undergo a security review before release.
- Regular HIPAA impact assessments help maintain secure and compliant healthcare applications over time.
Real Challenges of HIPAA-Compliant App Development — and How to Solve Them

There is a unique blend of regulations, app security, compliance, and user experience that must be managed when developing HIPAA-compliant healthcare apps. There are many operational and technical variables that healthcare app development teams must address, which can hinder product launch and increase compliance risk.
1. Balancing UX and Security
Stringent authentication and session management controls can be detrimental to usability. Workaround compliance tools such as Biometric Authentication, Adaptive MFA, and Security-Informed Workflows can help to remediate this issue.
2. Managing Third-Party Vendor Risk
Each healthcare integration increases compliance risk. Regular vendor audits, updated BAAs, and strict API security can reduce this risk.
3. Adapting to Evolving Regulations
Healthcare compliance requirements are always in flux. Organizations are best served by tracking updates from HHS and OCR and maintaining adaptable compliance documentation.
4. Scaling Securely
The more healthcare platforms expand and add app features, the more complex security becomes. Automated compliance testing, zero trust architecture, centralized logging, and infrastructure-as-code can efficiently maintain security as systems grow.
How Inventco Helps You Build HIPAA-Compliant Healthcare Apps?
Inventco builds HIPAA-compliant healthcare applications for startups, providers, and enterprises by combining healthcare expertise, regulatory knowledge, and scalable engineering. We develop applications that incorporate compliance, security, and PHI protection from the very first stage of the architecture, rather than integrating compliance in post-development stages.
Check My Mole, one of our innovations, is an AI-powered cancer detection application. It incorporates advanced backend architecture, UX/UI design, app testing, and intelligent diagnostic workflows. The application analyzes medical scans using AI and machine learning to aid early cancer detection. It enables predictive analysis and real-time reporting to medical personnel. For healthcare professionals, the application enables telemedicine for remote consultations with specialists.
Inventco provides organizations with an array of options, from secure cloud infrastructure and systems that are ready for audits to solutions that are compliant and AI-based, which enable them to develop innovative healthcare solutions and maintain scalable compliance rapidly.
Conclusion
The growth of the digital healthcare app market presents numerous business opportunities for companies specializing in safe, scalable healthcare app services. Healthcare solutions must be HIPAA-compliant, as patients’ healthcare data cannot be made public.
With increasing cybersecurity threats to healthcare integration, evolving mandates, and the need for enterprise-wide compliance with healthcare services, prevention is better than a cure. Comprehensive, deep structures within compliance for security, patient retention, and long-term operational support ensure continuous, stable revenue streams.
Instead of viewing HIPAA-compliant app development as a constraint, see it as an opportunity for your business. Adding in your app development the capability for compliant, secure, and scalable design from the early phases will decrease your legal risk, accelerate your adoption of enterprise customers, and give you a trustworthy healthcare platform.
The focus of your app will also determine your future growth. As healthcare compliance and technology advance together, the leading organizations will be those that provide secure, compliant digital experiences for healthcare consumers.
FAQ’s
Q1. What is a HIPAA-compliant healthcare application?
Ans. A HIPAA-compliant healthcare application protects patient health information through encryption, access controls, audit logging, and secure data transmission. It complies with HIPAA Privacy, Security, and Breach Notification Rules to ensure regulatory compliance and protect patient data.
Q2. Does every healthcare app need HIPAA compliance?
Ans. Not every healthcare app requires HIPAA compliance. Applications that handle, transmit, or store PHI for healthcare providers, insurers, or covered entities must comply, while general wellness or fitness applications without clinical integration are usually exempt.
Q3. How much does HIPAA-compliant app development cost?
Ans. HIPAA-compliant healthcare app development typically costs between $10,000 and $100,000+, depending on complexity, integrations, AI capabilities, security infrastructure, cloud services, compliance testing, and enterprise healthcare requirements for scalability and regulatory readiness.
Q4. What security features are essential for HIPAA compliance?
Ans. Healthcare applications require AES-256 encryption, secure authentication, MFA, RBAC, audit trails, session timeouts, breach monitoring, secure APIs, and end-to-end encryption to maintain HIPAA compliance and protect sensitive patient information.
Q5. Can AI-powered healthcare apps be HIPAA compliant?
Ans. Yes, AI-powered healthcare applications can remain HIPAA-compliant by using de-identified datasets, HIPAA-eligible cloud infrastructure, signed BAAs, secure AI workflows, encryption, and strict PHI access controls during model training and inference.